The new AI models signal a stronger push toward Microsoft-developed AI systems.

This Month's Tech Highlights
Trending Topics
The rapid evolution of Large Language Models (LLMs) is leading to specialized architectures and enhanced capabilities, particularly in areas requiring nuanced reasoning and robust security.
Key Points:
These developments highlight a trend towards more specialized, transparent, and autonomous LLM systems, moving beyond general-purpose conversational AI to tackle complex, real-world problems with greater precision and accountability.
As LLMs become more integrated into critical systems, the focus on their security vulnerabilities and the development of robust safety mechanisms is intensifying, particularly concerning prompt injection and harmful content generation.
Key Points:
These efforts underscore a critical need for advanced security frameworks and auditing methodologies to ensure LLMs operate safely and reliably, mitigating risks associated with malicious inputs and unintended outputs.
The global landscape of AI development is increasingly characterized by intense geopolitical competition, with nations vying for leadership and implementing strategic policies that impact the industry's direction.
Key Points:
These headlines demonstrate that AI is not merely a technological race but a critical component of national security and economic strategy, leading to diverse and sometimes contradictory policy decisions.
The ethical implications of AI, particularly concerning content generation, data privacy, and societal impact, are becoming central to development and deployment strategies, prompting new approaches to governance and control.
Key Points:
These instances reflect a growing recognition that ethical considerations and robust content moderation are paramount for the responsible development and societal acceptance of advanced AI systems, requiring interdisciplinary solutions.
The increasing reliance on digital infrastructure and the proliferation of advanced technologies, including AI, are making cybersecurity a paramount concern, with attacks targeting both individuals and major corporations.
Key Points:
These incidents underscore the critical need for enhanced cybersecurity measures across all layers of digital infrastructure, from personal devices to corporate networks, to protect against both financial and physical threats in an increasingly connected world.
Key Terms
Related Articles
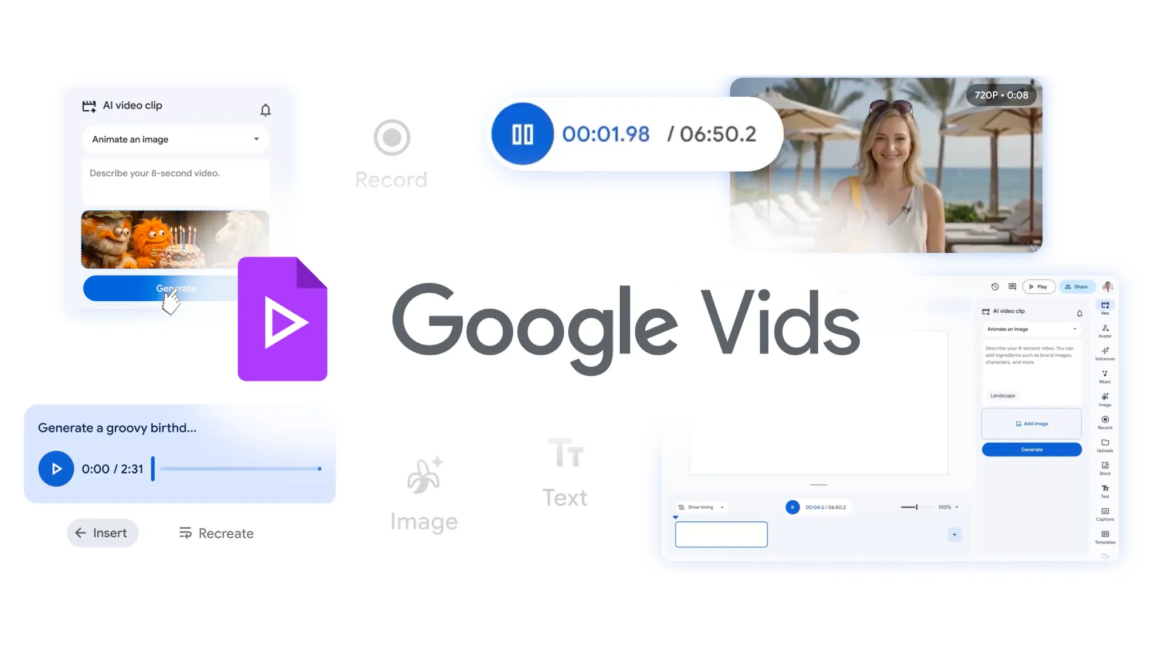
Google Vids brings together Google's most capable AI creation tools.
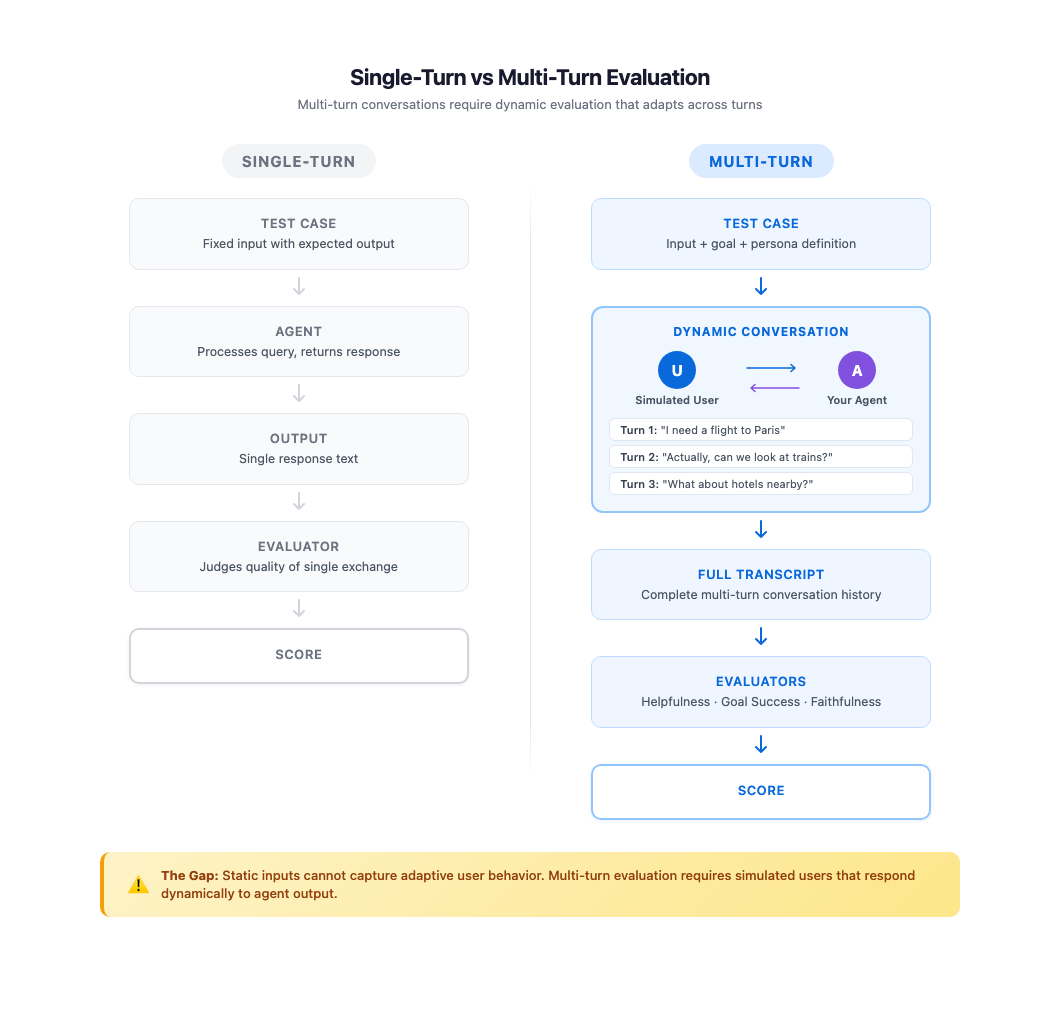
In this post, we explore how ActorSimulator in Strands Evaluations SDK addresses the challenge with structured user simulation that integrates into your evaluation pipeline.

Open models are driving a new wave of on-device AI, extending innovation beyond the cloud to everyday devices. As these models advance, their value increasingly depends on access to local, real-time c...
A decade ago, it would have been hard to believe that artificial intelligence could do what it can do now. However, it is this same power that introduces a new attack surface that traditional security...
Don’t deploy another model until you check out these essential LLMOps tools.
The Corelan tutorials helped shape how exploit development is learned worldwide and inspired generations of security researchers. Now you can watch them come to life. The post Exploit Writing Tutorial...
Think Anywhere in Code Generation
How context engineering and AI agents unlock real exploitation — not just recon — in penetration testing, red teaming, and bug bounty hunting. The “I Used AI for Pentesting” Fallacy The security commu...

AI benchmarks report how large language models (LLMs) perform on specific tasks but provide little insight into their underlying capabilities that drive their performance. They do not explain failures...
Topic: FreeScout Unauthenticated RCE via ZWSP .htaccess Bypass Risk: High Text:## # This module requires Metasploit: https://metasploit.com/download # Current source: https://github.com/rapid7/metaspl...

shared announcement blog post, we wanted to take a moment here to dive a little deeper. In this post, we’ll pull back the curtain on the benchmark itself, explore the methodology behind our choices, a...

This article is divided into three parts; they are: How Attention Works During Prefill The Decode Phase of LLM Inference KV Cache: How to Make Decode More Efficient Consider the prompt: Today’s weathe...
Lark CLI is the official command-line tool for Feishu/Lark Open Platform, covering 11 business domains with 200+ commands and 19 AI Agent Skills. Step-by-step guide from installation to real-world usa...
Authorization vulnerabilities are the most common critical finding in our API penetration tests. We find them on nearly every engagement: a user changes an ID in the URL and gets back another user’s d...
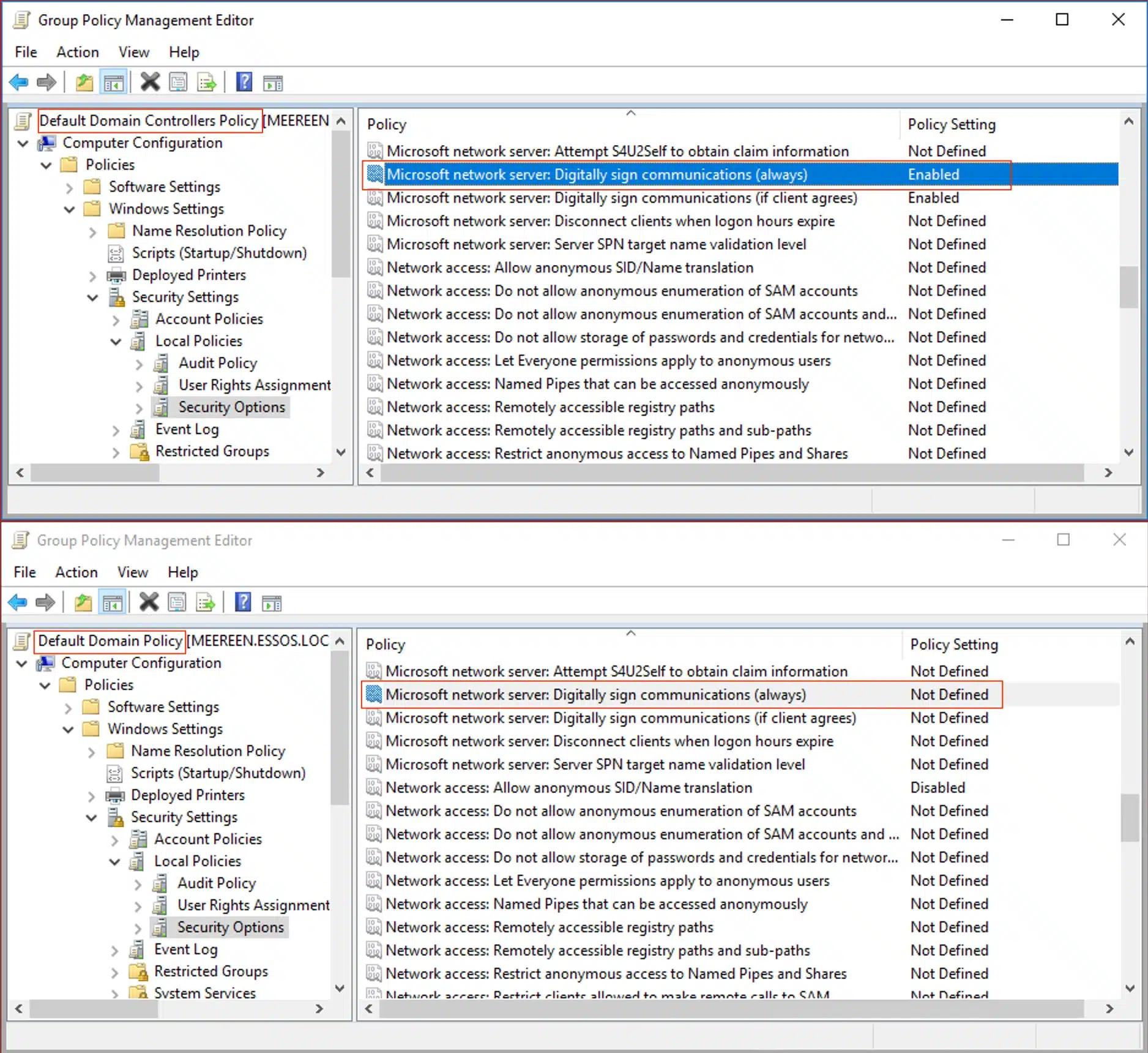
The False Sense of Security SMB signing on domain controllers has become standard practice across most Active Directory environments. But this hardening may have created a false sense of security. CVE...
Bishop Fox researchers took a deep dive into a new strongSwan vulnerability that allows unauthenticated attackers to take VPN services offline. We created an easy tool to test your strongSwan deployme...
Learn how QMD, a local hybrid search engine by Shopify founder Tobi Lütke, dramatically reduces AI agent token consumption through intelligent memory retrieval with BM25, vector search, and LLM rerank...
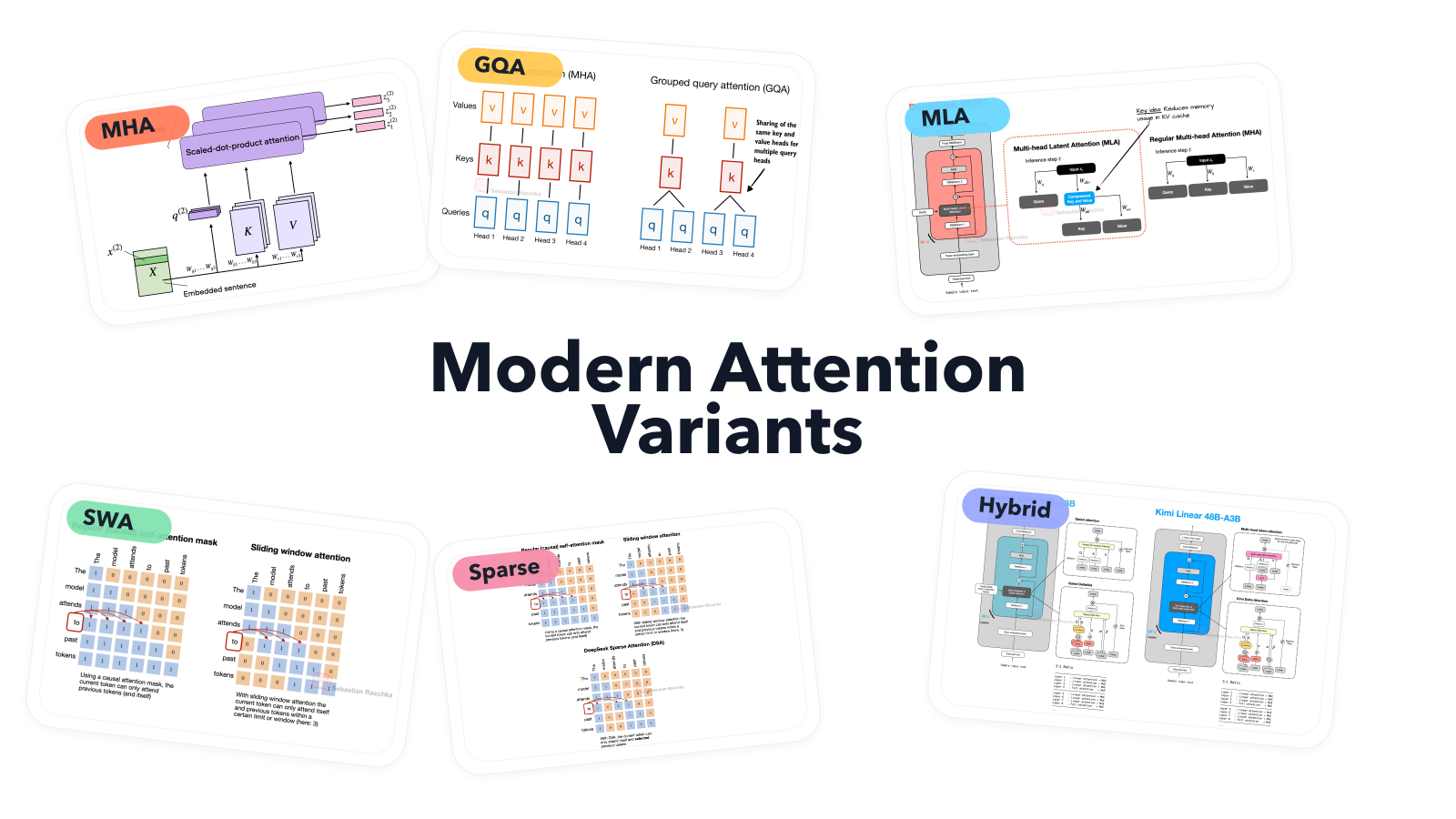
From MHA and GQA to MLA, sparse attention, and hybrid architectures
FunctionGemma is a specialized AI model for function calling. This post explains why fine-tuning is key to resolving tool selection ambiguity (e.g., internal vs. Google search) and achieving ultra-spe...


